Important
Powerpipe is now the preferred way to run this mod! Migrating from Steampipe →
All v0.x versions of this mod will work in both Steampipe and Powerpipe, but v1.0.0 onwards will be in Powerpipe format only.
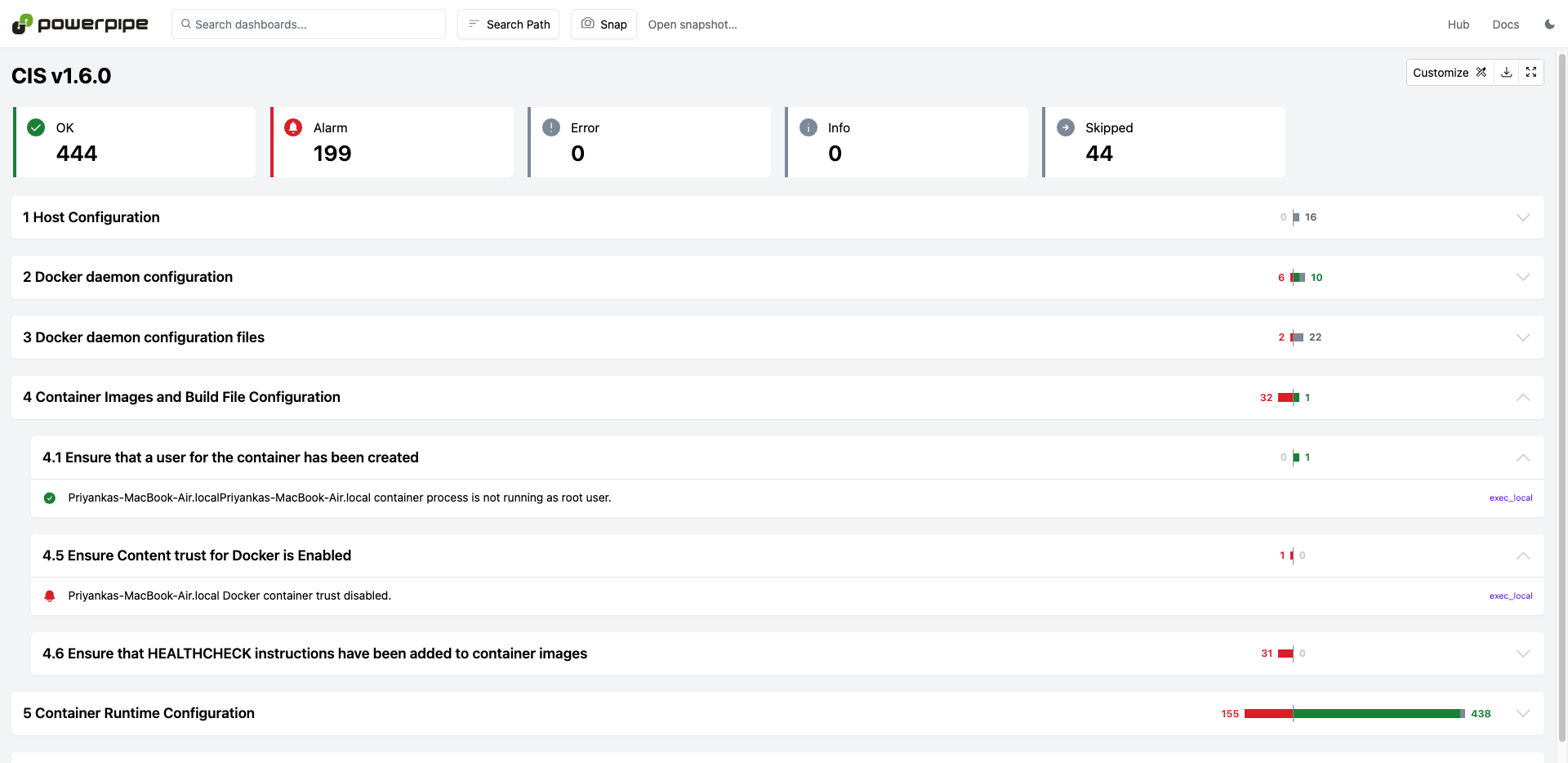
34+ checks covering industry defined security best practices for Docker. Includes full support for CIS v1.6.0 compliance benchmarks across all your Docker resources.
Includes full support for the CIS v1.6 Docker Benchmarks.
Install Powerpipe (https://powerpipe.io/downloads), or use Brew:
brew install turbot/tap/powerpipeThis mod also requires Steampipe with the Docker plugin and the Exec plugin as the data source. Install Steampipe (https://steampipe.io/downloads), or use Brew:
Install the Docker and Exec plugins with Steampipe:
brew install turbot/tap/steampipe
steampipe plugin install docker
steampipe plugin install execSteampipe will automatically use your default Docker credentials.
Finally, install the mod:
mkdir dashboards
cd dashboards
powerpipe mod init
powerpipe mod install github.com/turbot/steampipe-mod-docker-complianceStart Steampipe as the data source:
steampipe service startStart the dashboard server:
powerpipe serverBrowse and view your dashboards at http://localhost:9033.
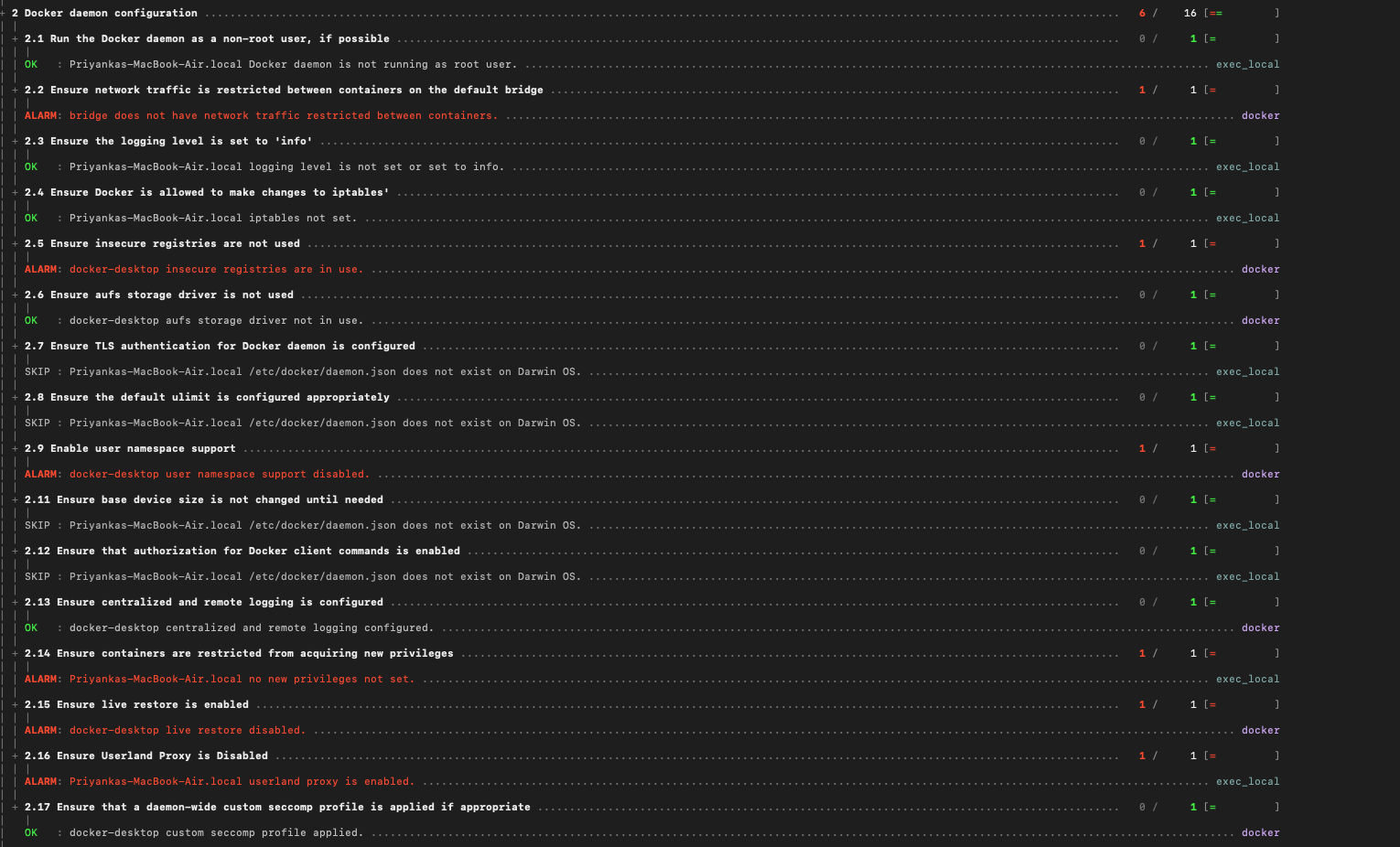
Instead of running benchmarks in a dashboard, you can also run them within your
terminal with the powerpipe benchmark command:
List available benchmarks:
powerpipe benchmark listRun a benchmark:
powerpipe benchmark run docker_compliance.benchmark.cis_v160_5Different output formats are also available, for more information please see Output Formats.
This mod uses the credentials configured in the Steampipe Docker plugin and the Steampipe Exec plugin. Please see below for examples on how to configure connections for these plugins.
When connecting to Docker on your local host, the Docker and Exec plugin connections require basic configuration:
connection "docker_local" {
plugin = "docker"
}
connection "exec_local" {
plugin = "exec"
}Note: It is not recommended to allow insecure connections. Please see Protect the Docker daemon socket for instructions on setting up TLS.
You only need to specify the host:
connection "docker_remote" {
plugin = "docker"
host = "tcp://12.345.67.890:2375"
}To connect to the remote host, you need to provide additional details in the Exec plugin connection, including the private key:
connection "exec_remote" {
plugin = "exec"
host = "12.345.67.890"
user = "ec2-user"
protocol = "ssh"
private_key = "/Users/myuser/keys/key.pem"
}If Docker does have TLS enabled, you will need to set tls_verify and provide a path to the directory containing your certificates and key files:
connection "docker_remote_tls" {
plugin = "docker"
host = "tcp://12.345.67.890:2376"
tls_verify = true
cert_path = "/Users/myuser/certs"
}The Exec plugin connection does not require any different configuration:
connection "exec_remote" {
plugin = "exec"
host = "12.345.67.890"
user = "ec2-user"
protocol = "ssh"
private_key = "/Users/myuser/keys/key.pem"
}If you have multiple local and/or remote Docker and Exec connections, you can use Steampipe workspaces to manage your Steampipe environments. Workspaces are profiles that are usually defined in ~/.steampipe/config/workspaces.spc.
For instance, if multiple Docker and Exec plugin connections were configured:
connection "docker_local" {
plugin = "docker"
}
connection "docker_remote_tls" {
plugin = "docker"
host = "tcp://12.345.67.890:2376"
tls_verify = true
cert_path = "/Users/myuser/certs"
}connection "exec_local" {
plugin = "exec"
}
connection "exec_remote" {
plugin = "exec"
host = "12.345.67.890"
user = "ec2-user"
protocol = "ssh"
private_key = "/Users/myuser/keys/key.pem"
}You can create multiple workspaces in ~/.steampipe/config/workspaces.spc:
workspace "docker_exec_local" {
search_path_prefix = "docker_local,exec_local"
}
workspace "docker_exec_remote" {
search_path_prefix = "docker_remote_tls,exec_remote"
}To switch between workspaces, you can use the --workspace argument:
powerpipe benchmark run cis_v160 --workspace docker_exec_local
powerpipe benchmark run cis_v160 --workspace docker_exec_remoteAdditional argments can be set in each workspace, including cache TTL, mod location, and more. Please see Workspace Arguments for a full list.
The Docker Compliance mod queries use the Docker and Exec plugin tables in order to retrieve information about the Docker Engine and the host it runs on. If you do not have access to connect to either of those, you can set the benchmark_plugins variable to decide which controls are included in benchmarks.
By default, both Docker and Exec queries are included:
benchmark_plugins = ["docker", "exec"]To only execute queries using Docker plugin tables, create steampipe.spvars with the following value:
benchmark_plugins = ["docker"]Note that controls can always be run directly, even if benchmark_plugins does not include the plugin type. For instance:
powerpipe control run cis_v160_5This variable can be overwritten in several ways:
-
Copy and rename the
steampipe.spvars.examplefile tosteampipe.spvars, and then modify the variable values inside that file -
Pass in a value on the command line:
powerpipe benchmark run cis_v160 --var 'benchmark_plugins=["docker"]' -
Set an environment variable:
SP_VAR_benchmark_plugins='["exec"]' powerpipe benchmark run cis_v160
This repository is published under the Apache 2.0 license. Please see our code of conduct. We look forward to collaborating with you!
Steampipe and Powerpipe are products produced from this open source software, exclusively by Turbot HQ, Inc. They are distributed under our commercial terms. Others are allowed to make their own distribution of the software, but cannot use any of the Turbot trademarks, cloud services, etc. You can learn more in our Open Source FAQ.
Want to help but don't know where to start? Pick up one of the help wanted issues: